According to Security Magazine, there are an estimated 2,200 cyberattacks each day in the United States. That amounts to around 91 attacks every hour or one attack every 39 seconds. In 2020, the average cost of responding to a cyberattack to businesses of all sizes was estimated to be $3.86 million. As our work, school, and healthcare moves online, the need to prevent cyberattacks will become more pronounced.
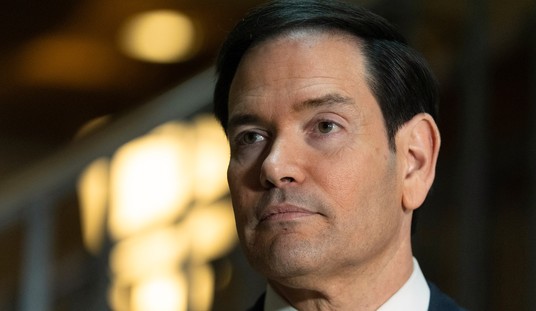
Recognizing the significant threat cyberattacks pose, a bipartisan group of U.S. Senators, led by Senator Mark Warner (D-VA), introduced the Cyber Incident Notification Act (CINA). While the bill fails to provide comprehensive protections offered in Europe, the United Kingdom, or Canada, CINA nevertheless represents an essential first step toward ensuring the U.S. has a robust toolkit to prevent cyberattacks and fully protect consumer data.
Despite the significant threat cyberattacks present, there are very few federal laws governing cybersecurity in the United States. Instead, rules governing cybersecurity are either left to the individual states or industry-specific. Leaving data privacy to the states creates inconsistent protections, while industry-specific legislation leaves millions without appropriate protections.
Examples of industry-specific data security and privacy rules laws include the 1996 Health Insurance Portability and Accountability Act (HIPAA), requiring patients to be notified within 60 days that their medical information has been compromised, and the 1999 Gramm-Leach-Bliley Act, which requires financial institutions to explain how they “safeguard sensitive data.”
Under the proposals outlined by CINA, federal agencies and owners of critical infrastructure, such as fuel pipelines or communications centers, would have to notify the federal government that they have been subject to a cyberattack within 24 hours. In addition, included in the required report, agencies and owners of critical infrastructure must state whether they believe the attack was initiated by another nation-state, a persistent cyberattacker, or a global organized crime group.
Recommended
They must also report whether the attack could compromise “national security interests, foreign relations, or economy of the United States or to the public confidence, civil liberties, or public health and safety of people in the United States.”
Failure to comply with CINA carries substantial penalties. Entities subject to CINA without government contracts would be “subject to financial penalties equal to 0.5 percent per day of the entity’s gross revenue,” while those with government contracts face the prospect of penalties that “may include removal from the Federal Contractor Schedules.” In addition, federal agencies will face a referral to the Inspector General with the matter to be treated as an “urgent concern.”
When it comes to protecting data, rapid notification is important. When consumers are notified early that their data might have been stolen in cyberattacks, they can take steps early to mitigate the potential damage, such as closing credit cards or changing passwords. On the other hand, late notification effectively grants criminals free use of this sensitive information- often without the consumers’ knowledge that they are victims.
Unfortunately, the consumer protections offered CINA are limited due to the fact the proposal only covers critical infrastructure and federal agencies. In addition, excluded from complying with CINA are private companies that hold significant amounts of often sensitive consumer data. CINA’s limited scope means that notification requirements will still matter for state governments with varying and often limited notification requirements.
Most states, for example, do not provide a specific time frame for consumers or the state government to be notified, instead only requiring that they be notified “without unreasonable delay.” Moreover, where notification timeframes do exist, states do not mandate they occur within 24 hours. Vermont, for example, only requires consumers and the state government to be notified within 45 days, while in Connecticut that time frame is 90 days.
Additionally, there is no requirement that consumer reporting agencies be notified unless the breach affects a certain number of data points. In North Carolina, that number is 1,000, but in Texas, the number is 10,000. These requirements mean that potentially thousands of consumers will never know their data has been compromised.
The fact that state governments have such limited reporting requirements that leave consumer data vulnerable should be incentive enough for Congress to expand the provisions of CINA to cover all data breaches, not just federal agencies or critical infrastructure.
While there is much work to be done in the realm of data breach notification, passing CINA would be an important first step to ensuring American consumers enjoy robust protection from cyberattacks. Without these protections, Americans will continue to be vulnerable to cybercriminals.
Congress should get CINA on President Biden’s desk as soon as possible and work on a federal data breach notification law that expands CINA’s provisions to private entities that are entrusted with sensitive data.
Edward Longe is a Policy Manager at the American Consumer Institute, a nonprofit educational and research organization. For more information about the Institute, visit www.TheAmericanConsumer.org or follow us on Twitter @ConsumerPal.























Join the conversation as a VIP Member